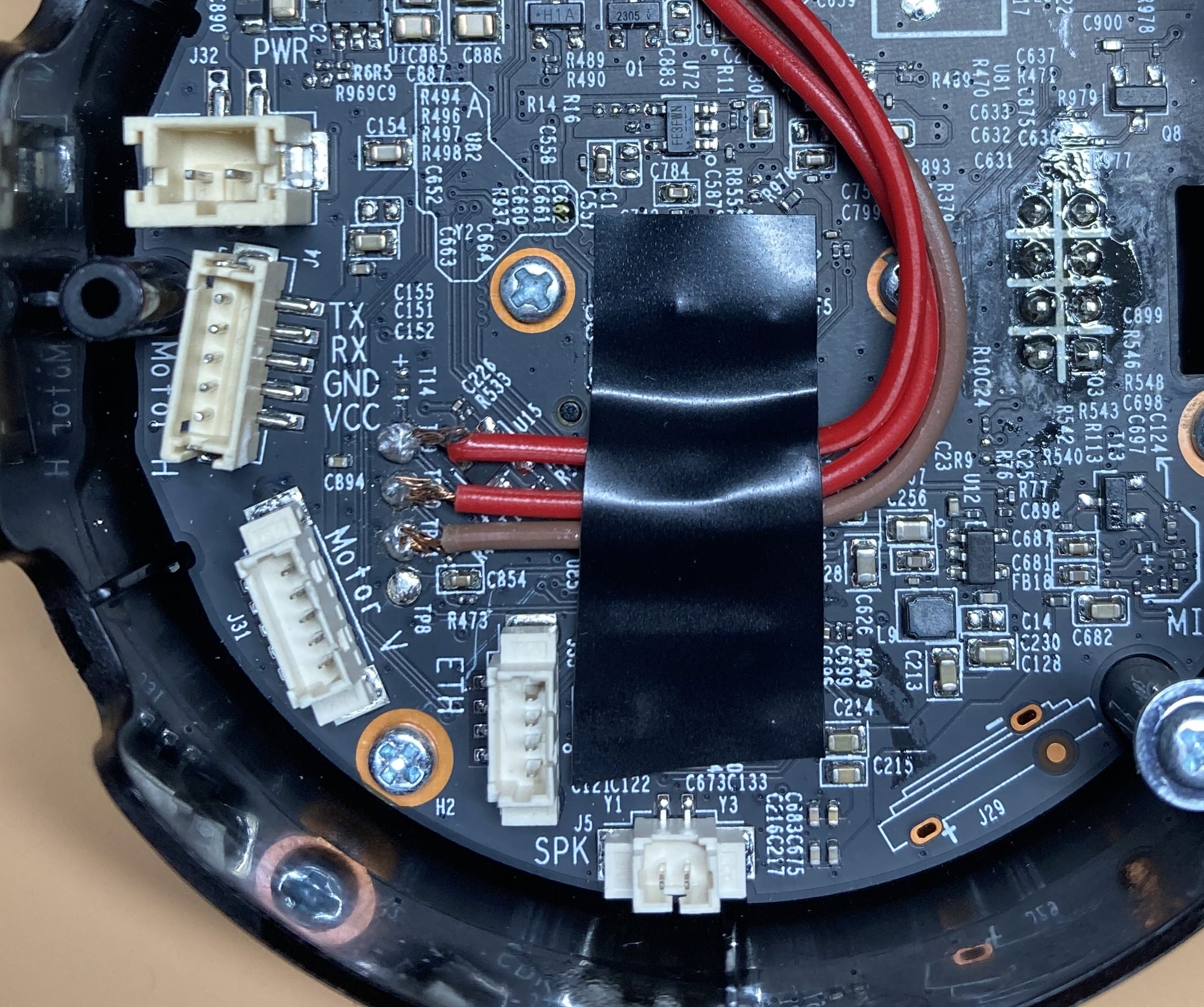
Hello there. Today I would like to share with you my first CVE, which corresponds to a command injection vulnerability found a couple months ago in the TP-Link Tapo c200 camera, that allows an attacker to take full control of the device with root privileges. It was assigned CVE-2021-4045 by the INCIBE, and you can check the official advisory here. The vulnerability affects all firmware versions prior to 1.1.16 Build 211209 Rel. 37726N, so if you own this model, I suggest you update it.

Hacking into Wi-Fi Camera TP-Link Tapo C200 (CVE-2021–4045), by LeoX
GitHub - soosmile/POC

TP-Link Tapo C320WS Outdoor Security Wi-Fi Camera
Remote Code Execution Vulnerabilities Found in TP-Link, NetComm Routers - SecurityWeek

Exploitdb - TP-Link Tapo c200 1.1.15 - Remote Code Execution

TP-Link Tapo Pan/Tilt Security Camera for Baby Monitor, Pet Camera w/ Motion Detection, 1080P, 2-Way Audio, Night Vision, Cloud & SD Card Storage, Works with Alexa & Google Home (Tapo

TP-Link Tapo c200 Camera Unauthenticated RCE (CVE-2021-4045) - hacefresko
Findings / Shell access · nervous-inhuman tplink-tapo-c200-re · Discussion #6 · GitHub
Findings / Shell access · nervous-inhuman tplink-tapo-c200-re · Discussion #6 · GitHub
TP-Link Tapo c200 Camera Unauthenticated RCE (CVE-2021-4045) - hacefresko

Joşé Mąríą A. on LinkedIn: TP-Link Tapo c200 Camera Unauthenticated RCE (CVE -4045-2021)
PocOrExp_in_Github/2021/README.md at main · ycdxsb/PocOrExp_in_Github · GitHub

Hacking into Wi-Fi Camera TP-Link Tapo C200 (CVE-2021–4045), by LeoX